Client Situation
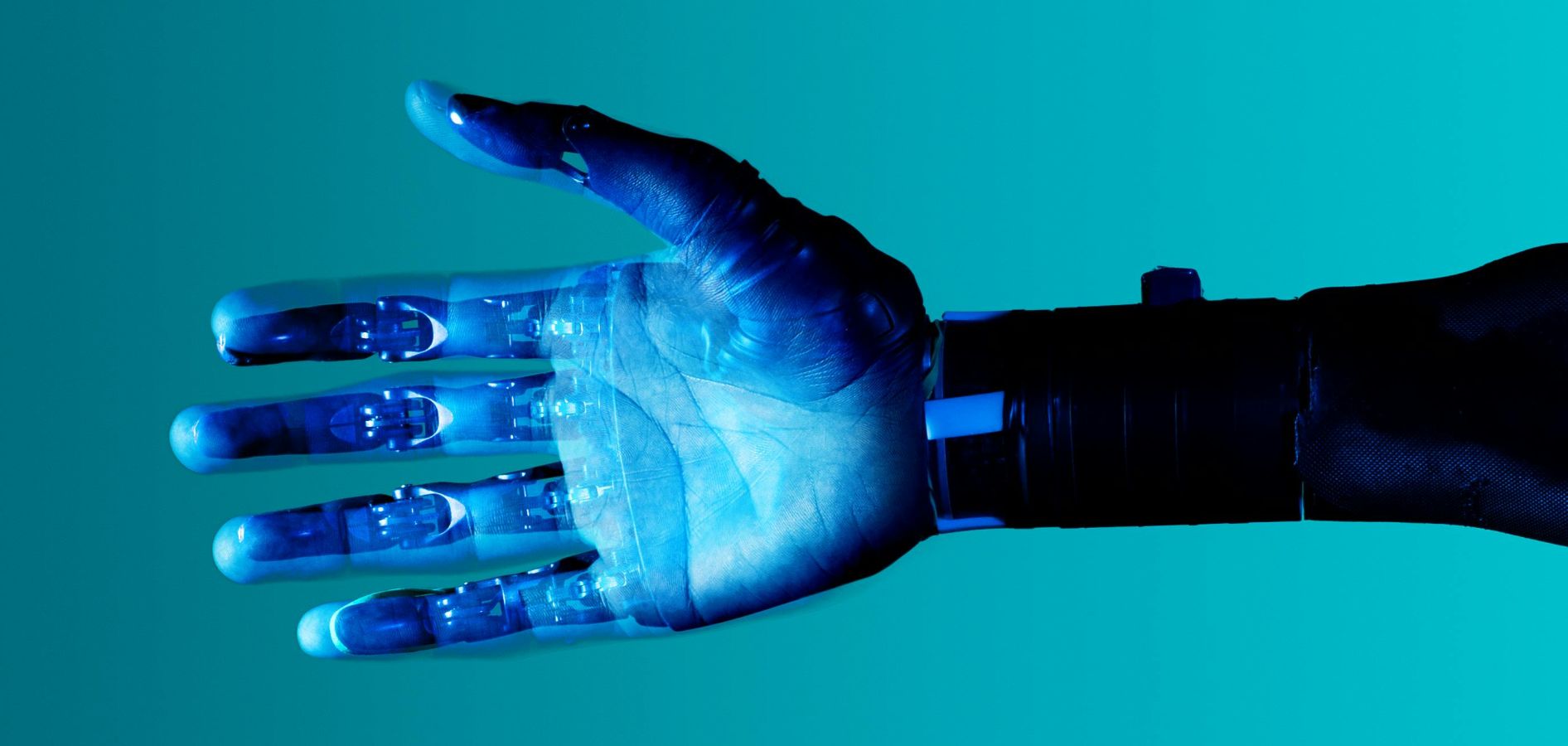
A European technology company sought to introduce a palm vein biometric identification system to the United States, based on an advanced infrared scanning SDK originally developed by Fujitsu. The system used near-infrared light to map the unique vein patterns inside the human palm, creating a biometric identifier that is internal, non-visible, and extremely difficult to replicate.
Unlike fingerprint or facial recognition systems, this technology:
-
Does not rely on latent prints or external features
-
Cannot be easily spoofed using lifted fingerprints or images
-
Does not leave behind usable biometric traces on surfaces
-
Reduces long-term risk, as biometric data cannot be reverse-engineered from residual evidence
These characteristics made the solution highly relevant for defense, banking, healthcare, and large-scale public venues. However, entering the U.S. market required overcoming significant barriers related to adoption, integration, and trust in a space dominated by more familiar biometric modalities.
Strategic Challenge
The client needed to:
-
Establish credibility in a market accustomed to fingerprint and facial recognition systems
-
Demonstrate clear advantages in both security and usability
-
Integrate the technology into real-world applications across multiple industries
-
Navigate procurement environments in both commercial and government sectors
-
Generate early traction with high-visibility use cases
Additionally, the solution required education of stakeholders, as its advantages, particularly around anti-spoofing and privacy, were not widely understood.
Our Approach
We designed and executed a U.S. market entry strategy focused on high-impact use cases, ecosystem integration, and institutional validation.
1. Positioning Around Security and Privacy Advantages
We reframed the technology not simply as another biometric solution, but as a next-generation identity platform addressing critical weaknesses in existing systems.
Key differentiators emphasized:
-
No latent biometric trace (unlike fingerprints used in forensics)
-
No reliance on stored facial images
-
Strong resistance to spoofing and replication
-
Enhanced privacy and reduced long-term risk in case of data breaches
This positioning resonated strongly in sectors where security and privacy are paramount.
2. Integration Across Multiple Systems
We supported the deployment of the technology across a wide range of applications, embedding it into:
-
Network infrastructure and secure authentication systems
-
Encryption and data security frameworks
-
Biometric access control solutions
-
Time and attendance systems
-
Ticketing and identity verification platforms
-
Account login and identity management systems
This demonstrated the versatility and scalability of the platform across industries.
3. Focus on Three High-Impact Use Cases
To accelerate adoption, we concentrated on three core applications where the technology delivered immediate and visible value:
A. Stadium Access and Crowd Flow Optimization
We implemented the system in large-scale venue environments, enabling:
-
-
Faster throughput than traditional ticket scanning or barcode systems
-
Seamless, contactless entry using palm authentication
-
Real-time identification and prevention of banned individuals entering venues
-
This created a superior user experience while enhancing security and operational efficiency.
B. Cashless, Touchless Payment Systems
We deployed the technology as a biometric payment solution, allowing users to:
-
-
Authenticate transactions using only their palm
-
Eliminate the need for cards, devices, or physical tokens
-
Link identity to prepaid or debit accounts for seamless payments
-
This approach combined convenience with high security, particularly in environments such as stadiums, healthcare facilities, and secure campuses.
C. Critical Infrastructure Access Control
We introduced the system into industrial and high-security environments where:
-
-
Non-invasive, contactless identification was required
-
Traditional biometrics posed risks due to latent traceability
-
High assurance identity verification was essential
-
The technology provided secure access control without leaving behind exploitable biometric data, making it particularly suitable for defense-related and sensitive infrastructure applications.
4. Institutional Validation and Strategic Demonstrations
To build credibility at the highest levels, we facilitated presentations and engagements with key institutional stakeholders.
This included showcasing the technology at the NATO Communications and Information Agency, demonstrating its relevance for defense and security applications.
We also supported deployments with U.S.-based defense contractors and suppliers, including installations in Virginia, creating strong reference points within the defense ecosystem.
The Outcome
The market entry strategy resulted in significant traction across multiple sectors:
-
Successful deployment of palm vein biometric systems in the United States
-
Adoption across stadiums, payment systems, and critical infrastructure environments
-
Integration into a wide range of security and identity management applications
-
High-level validation through engagement with defense and institutional stakeholders
-
Establishment of strong reference cases within U.S. government and commercial sectors
Strategic Impact
The project positioned the client as a leader in advanced biometric identification, differentiating it from traditional solutions through a combination of security, privacy, and usability.
Key impacts included:
-
Accelerated adoption in high-security and high-throughput environments
-
Increased trust among institutional and enterprise clients
-
Expansion into multiple verticals with scalable applications
-
Strengthened credibility through defense-sector engagement
Key Insight
In biometric security, the next frontier is not just accuracy, but resilience and privacy. By consistently educating the market about the latest shift in technology and the risks involved in reliance on previously accepted external, reproducible identifiers, a whole new market opens up for a new technology. Success depends on strategic positioning.
